CDW Newsroom
FEATURED
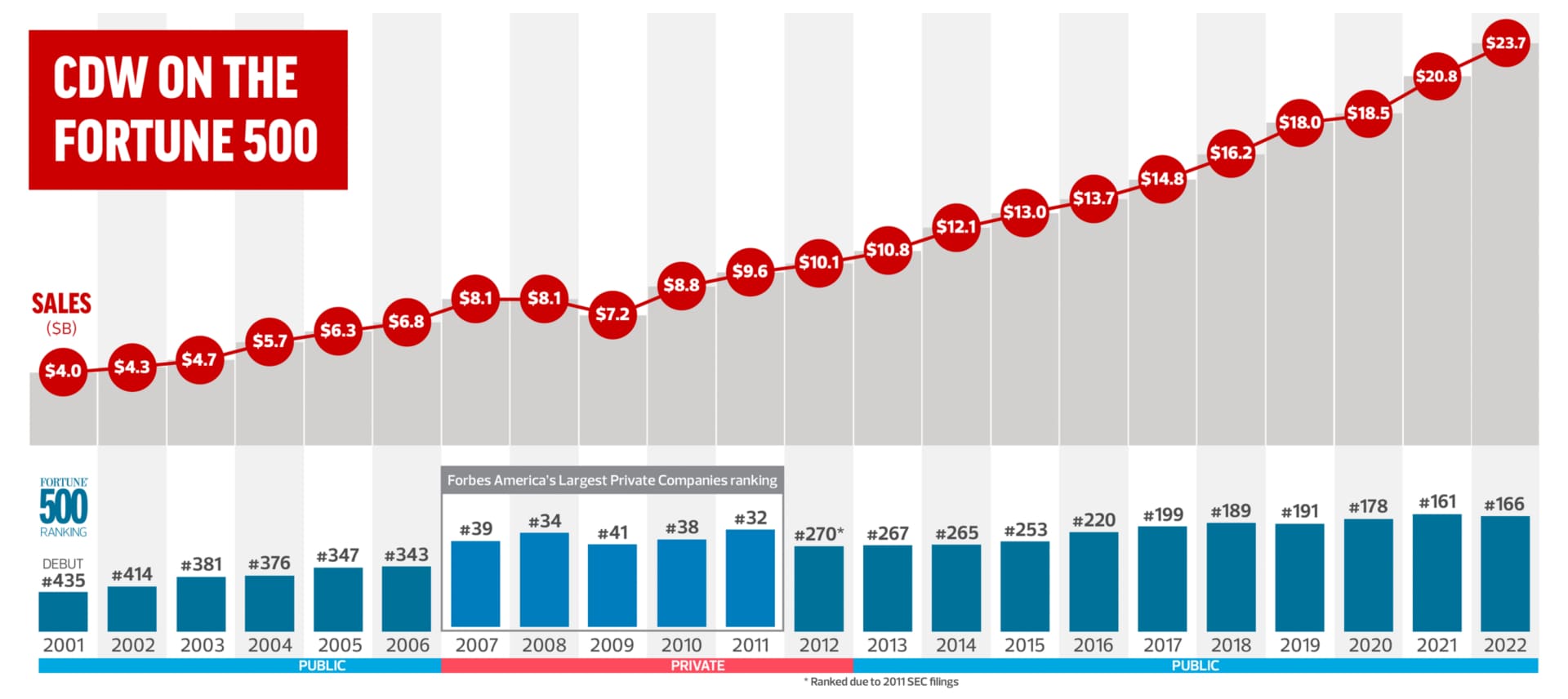
CDW on the Fortune 500
Contact Us
We welcome media inquiries. Please provide your contact information and story details, including your deadline, and we'll be in touch.
CDW Public Relations
mediarelations@cdw.com
CDW Analyst Relations
analystrelations@cdw.com
CDW Spotlight Blog
PARTNERS | SPOTLIGHT BLOG
CDW Named Major Player in IDC MarketScape for Cybersecurity Consulting Services
Tech Insights
INDUSTRY SPECIFIC | TECH INSIGHTS
Securing Higher Education – It Takes Two
SOLUTIONS | TECH INSIGHTS
CDW Digital Workspace Solutions Report
SOLUTIONS | TECH INSIGHTS
The Power of Priority: Strategies for IT Innovation
Press Releases
APRIL 17, 2023
CDW to Announce First Quarter 2024 Results on May 1
FEBRUARY 7, 2023
CDW Authorizes $750 Million Share Repurchase Program Increase and Declares Quarterly Cash Dividend of $0.62 Per Share
FEBRUARY 7, 2023
CDW Reports Fourth Quarter and Full Year 2023 Earnings
NOVEMBER 14, 2023
CDW to Participate in the UBS Global Technology Conference
NOVEMBER 1, 2023
CDW Increases Quarterly Cash Dividend 5% to $0.62 Per Share